Real Impact. Really Different Approach to Workplace Compliance Training.
Online HR and compliance workplace training that drives change and is easy to use – backed by compliance expertise.


Relatable, compliant, and interactive online training to
create positive workplace culture
Engaging Content
- Interactive relevant training through real life skill building examples.
- Modern course design with opportunities for brand customization.
- Mobile First, employees can take their course wherever, whenever.


Compliance Expertise
- Stay ahead of legal developments with in-house attorneys dedicated to workplace compliance and monitoring workplace legislation daily – so you don’t have to.

Data & Reporting
- Spend less time administering trainings while measuring the outcomes that matter with a solution tailored to your organizations needs.

Explore Our Most Popular Workplace Compliance Training Courses
Stay compliant with state and local mandates, including CA, IL, CT, NY, and NYC, and provide employees a fresh approach to sexual harassment training.
Promote civility, equity, and respect within multicultural and global workforces.
Provide guidance on high-risk situations to teach employees what to avoid.
Encourage your workforce to examine key concepts like identity, power, and privilege through real life scenarios.
Define ethical standards and establish expectations for employee behavior in the workplace.
Teach your employees about the European Union’s GDPR and its requirements.
Drive a deeper understanding of bias and the negative effect it has on workplace culture.
Specify your code of conduct as defined by your organization and promote a more ethical workplace.
Educate managers on how to lead inclusive teams where employees thrive.
1,200+ Companies Build Better Workplace Cultures With EVERFI





1,200+ Companies Build Better Workplace Cultures With EVERFI




























































Everfi is the trusted online training partner you need
Invest in your people to guide your business growth. Join the hundreds of organizations that use EVERFI to
build engaged, high-performance teams.

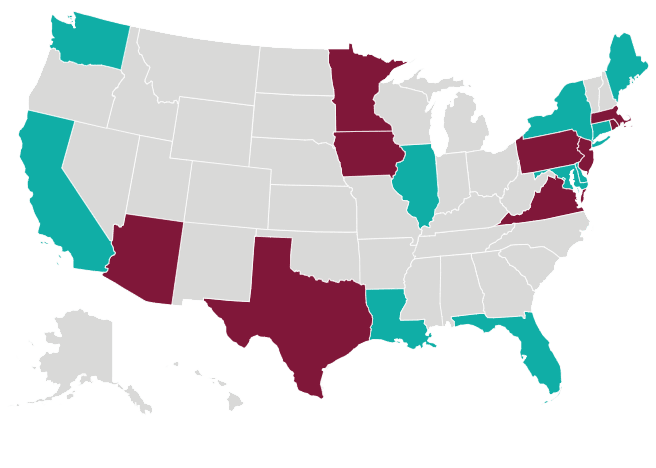
Pending | Enacted
Which States Require Harassment Training?
A new legislative landscape and a desire to stay out of a potential harassment spotlight are forcing employers to rethink their sexual harassment prevention strategy.





